Creating Constrained Certificate Authorities
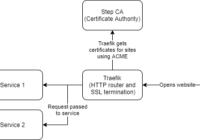
This blog post has been written in collaboration with Mohit Gupta whose blog covers cybersecurity and other random technical things. For our home labs, we have a number of internal systems shared between the two of us including a number of web services. Originally, these were accessed over plaintext HTTP connections, or bypassing any certificate… Read More »